What is SSH and how to use SSH in Linux

The digital environment works on a secure platform. SSH is one of the networking interfaces that provide a Secure Shell. ...
Read more
How to Restore Deleted Contacts From Google

Google accounts give a lot of facilities to users for storing their personal information. Contacts are the basic needs that ...
Read more
How to add business in google map

The business sector wholly changed into digital form. Users can interact with business providers all around the world. Users can ...
Read more
How to share the screen in Google meet

Google Meet is one of the best meeting platforms in digital mode. In the digital mode, users can create the ...
Read more
How to create a Google Meet link and share

Digital platforms make our life in a comfort zone. Google meet is one of the best services given by Google ...
Read more
How to fix leverage browser caching in PageSpeed insights

The cache is a mechanism that operates between the web server and web browser. Generally, cache stores multiple copies to ...
Read more
How to create an email template in Gmail

Email templates are the design and the layout that is pre-installed in the email whenever you want to access and ...
Read more
How to create Apple ID login and Sign in Apple iPhone with Apple ID?
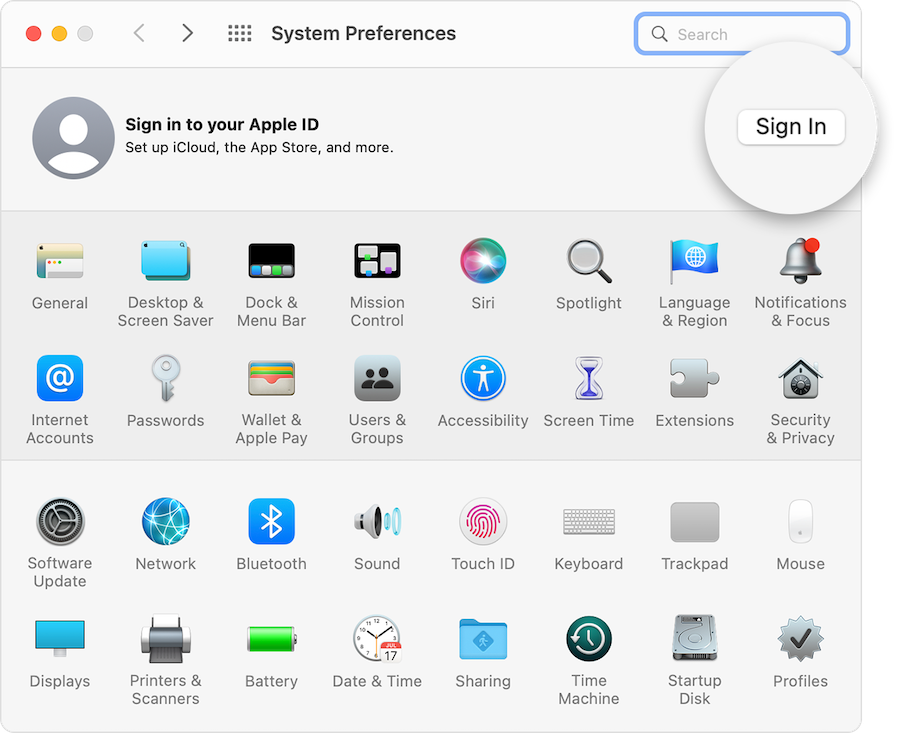
Apple ID is a unique ID that provides a special identity to your device. To Sign in to the Apple-based ...
Read more
How to delete Google account

Google provides a lot of services. Android smartphone apps can access via a Google account. Users need to break this ...
Read more
How to enable two-steps verification in google
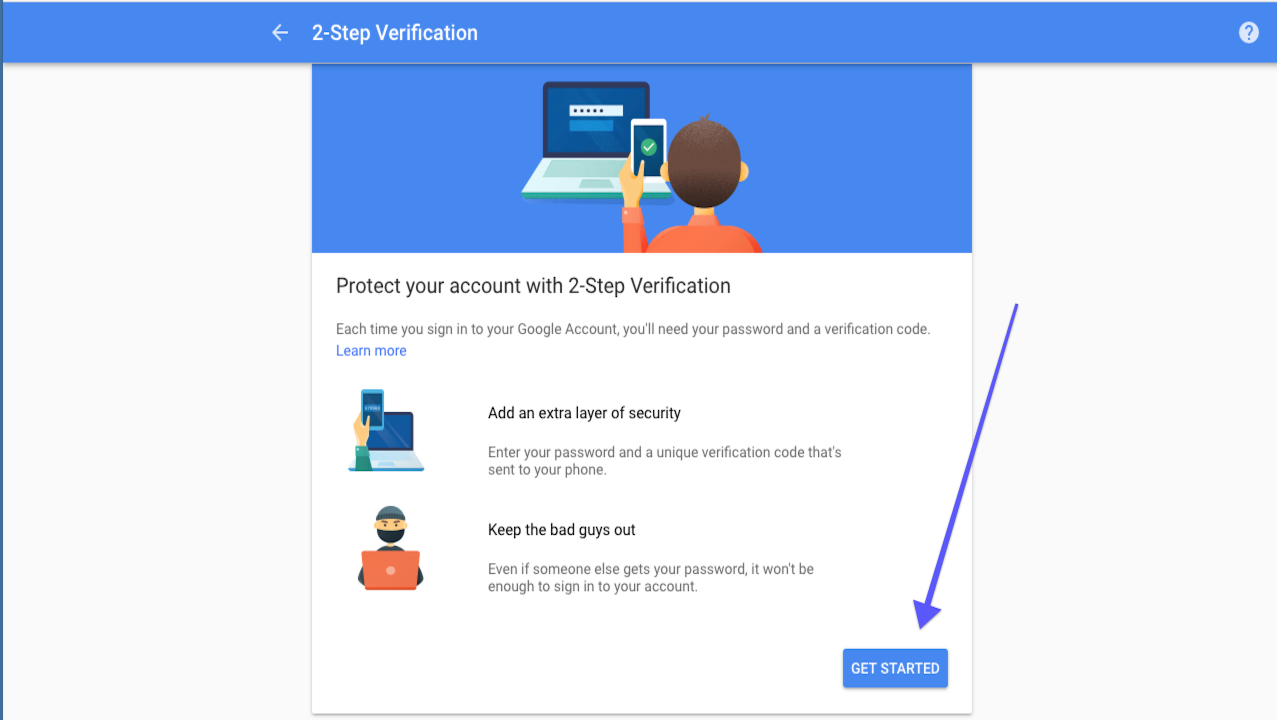
“Google Authenticate not only user life but safe from an unknown party Information you retrieve, be safe –be defend“ The operating ...
Read more




